Add file protocol account
If you want to use SMB, FTP, SFTP or WebDAV file protocols, you have to either have access to server or install and configure one on your own. Explaining how to setup and configuring a server is not in the scope of this help text, but there are many guides on the internet.
Typically Linux, OSX and Windows come with built-in SFTP or SMB server software. Also many NAS vendors ship some or all of the mentioned file protocols as part of the NAS software package.
We will explain the configuration options for the various file protocol account types below.
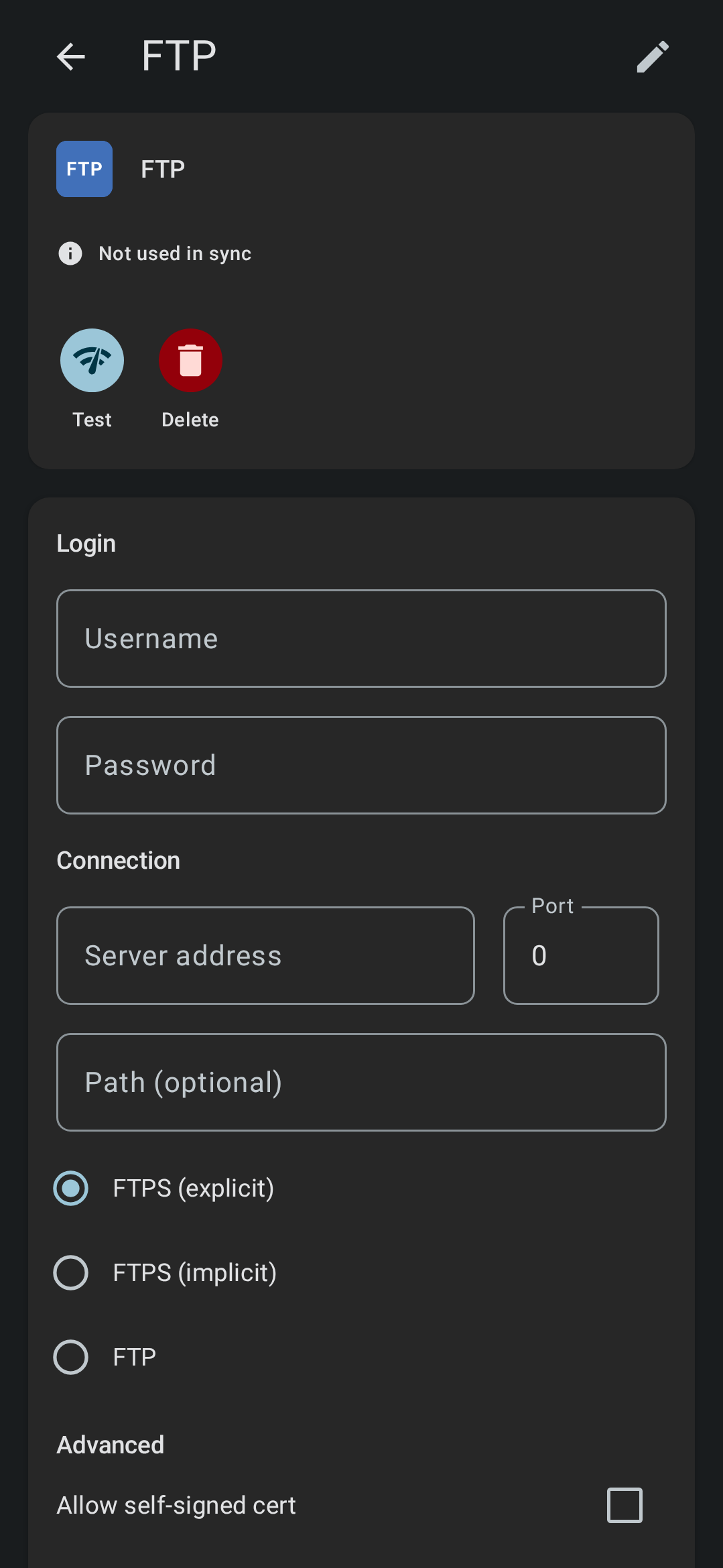
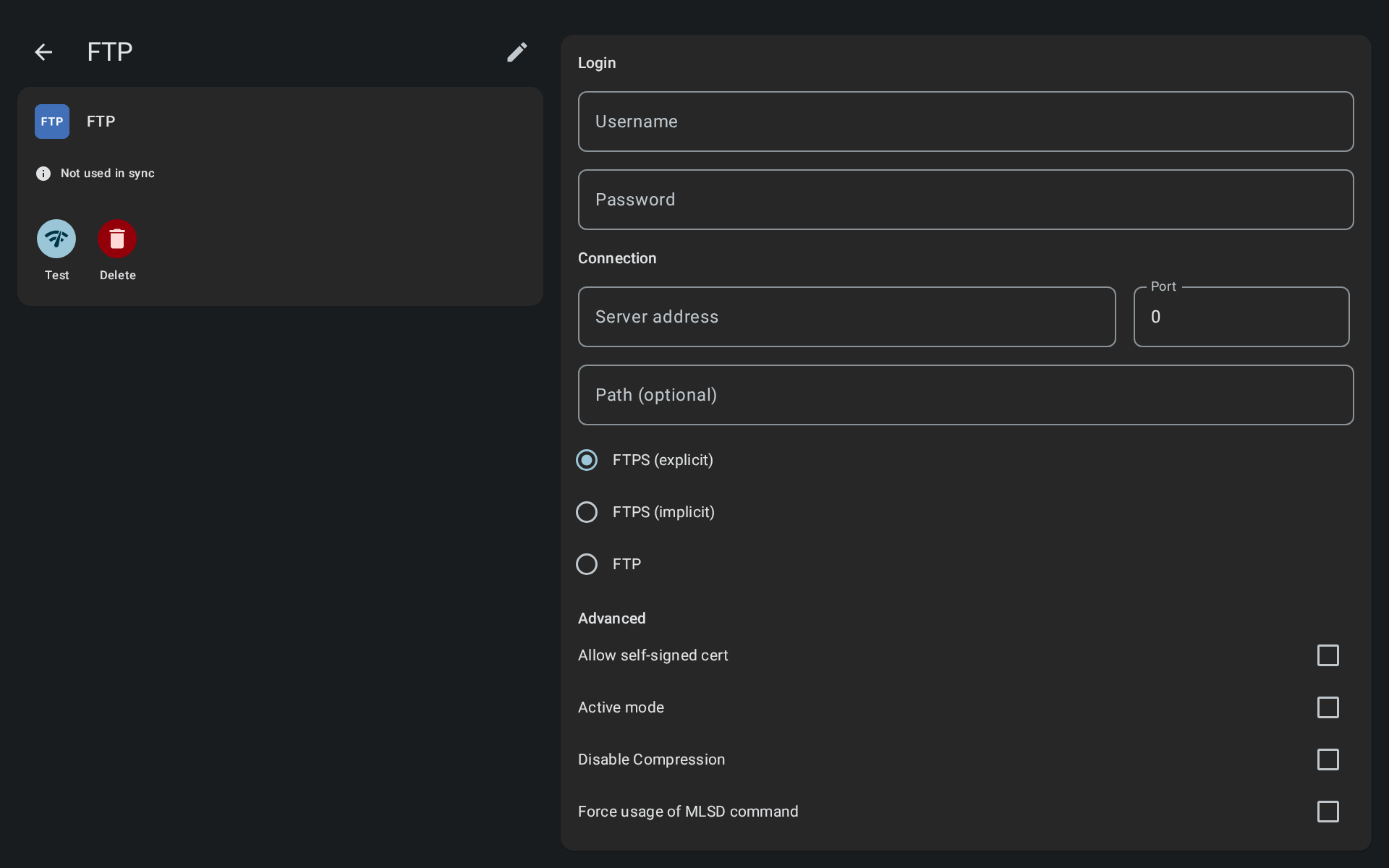
FTP
The File Transfer Protocol (FTP) is a standard communication protocol used for the transfer of computer files from a server to a client on a computer network.
- Login name: Your username for the server.
- Password: Your password for the server.
- Server address: The IP address or hostname of the server (without protocol or path), so like “192.34.243.2” or “my.server.com”.
- Port: The port to use.
- Path (optional): Optional path on the server that the connection should open on connection.
- Connection type: Choose plain FTP, explicit FTPS (recommended) or implicit FTPS (not recommended).
- Allow self-signed cert: Enable if you use a self-signed SSL certificate on the server.
- Active mode: To enable FTP active mode.
- Disable compression: To disable stream compression.
- Force usage of MLSD command: Force listing of FTP folders to use MLSD command, this can be useful for servers that support this command but doesn’t let the client know.
- FTP engine: If ftp connection is not working, you can try to use a different FTP library for access. Only the default edtFTPj/PRO engine has support for SSL session resumption.
- Charset: The charset that the server uses to return with.
- Connection timeout: The time period within which a connection between a client and a server must be established before error is registered.
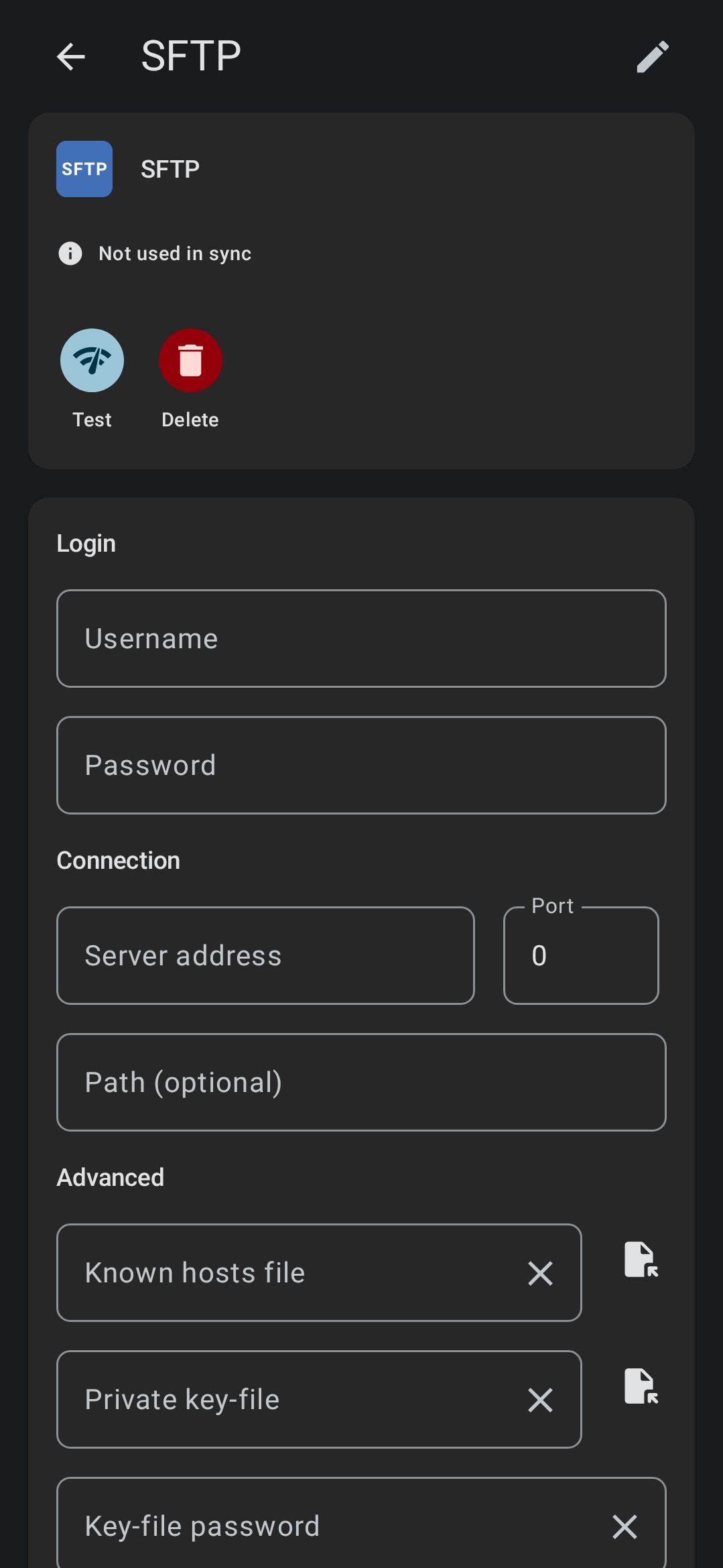
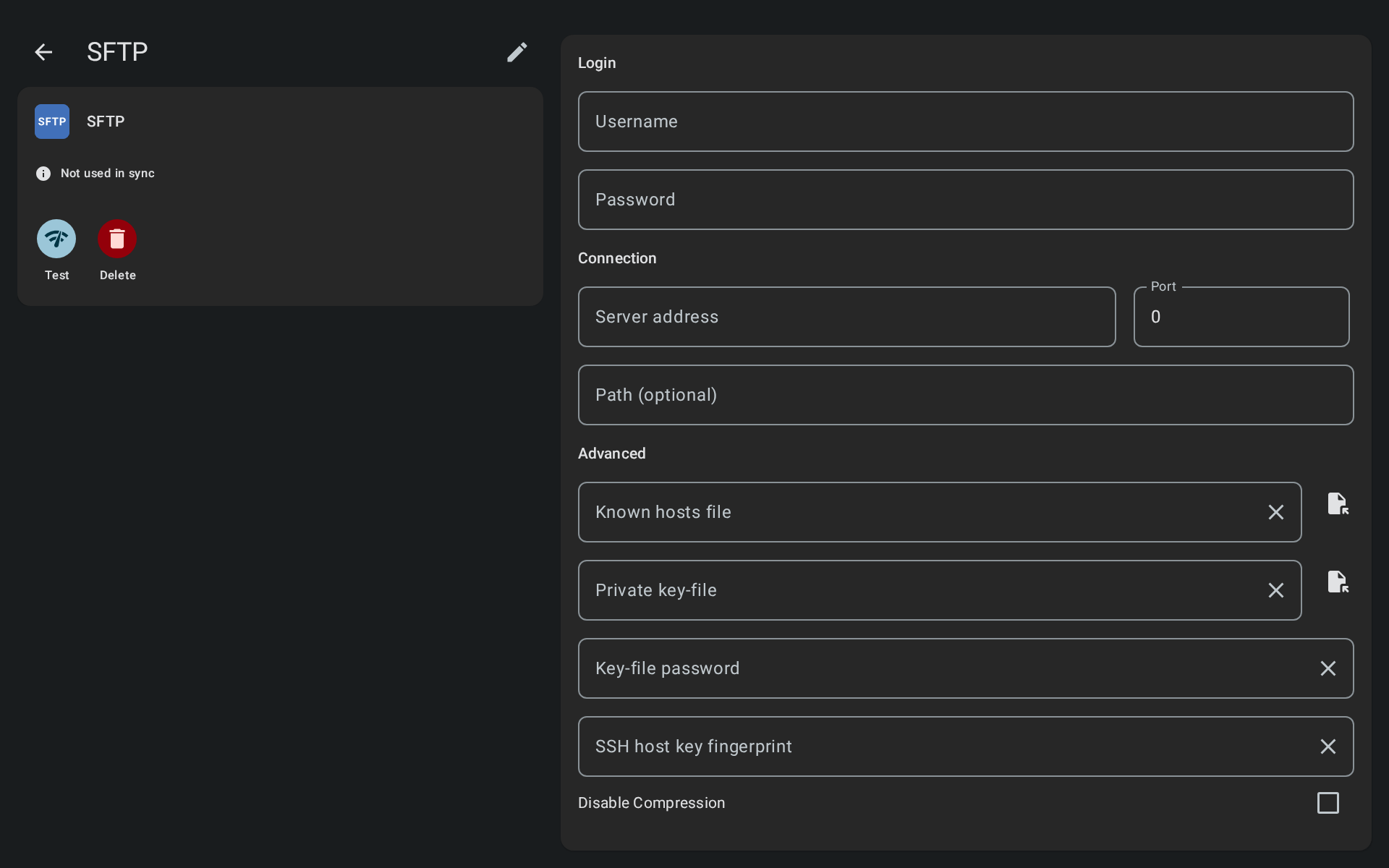
SFTP
SFTP (SSH File Transfer Protocol) is a secure file transfer protocol. It runs over the SSH protocol.
- Login name: Your username for the server.
- Password: Your password for the server.
- Server address: The IP address or hostname of the server (without protocol or path), so like “192.34.243.2” or “my.server.com”.
- Port: The port to use.
- Path (optional): Optional path on the server that the connection should open on connection.
- Host key fingerprint: The host key fingerprint, this will be pre-filled when you test account. If the host key changed connection will fail until you update the fingerprint again.
- Known hosts file: Known host file - supply this if you want to ensure connection can only be made to the specified servers in the file.
- Private key-file: A private key file used for authentication in addition to or instead of username/password.
- Key-file password: The password to access the private key file.
- Disable compression: To disable stream compression.
- Charset: The charset that the server uses to return with.
- Connection timeout: The time period within which a connection between a client and a server must be established before error is registered.
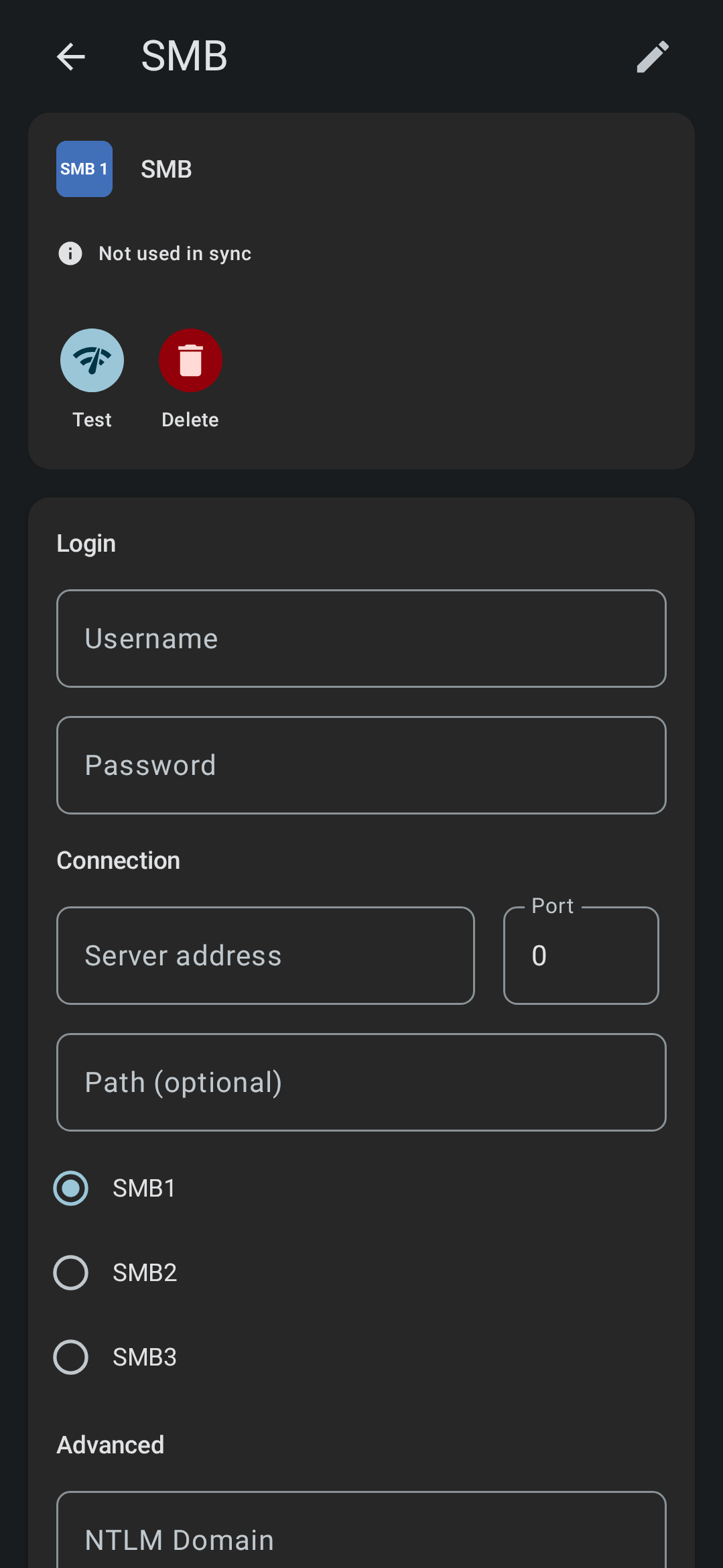
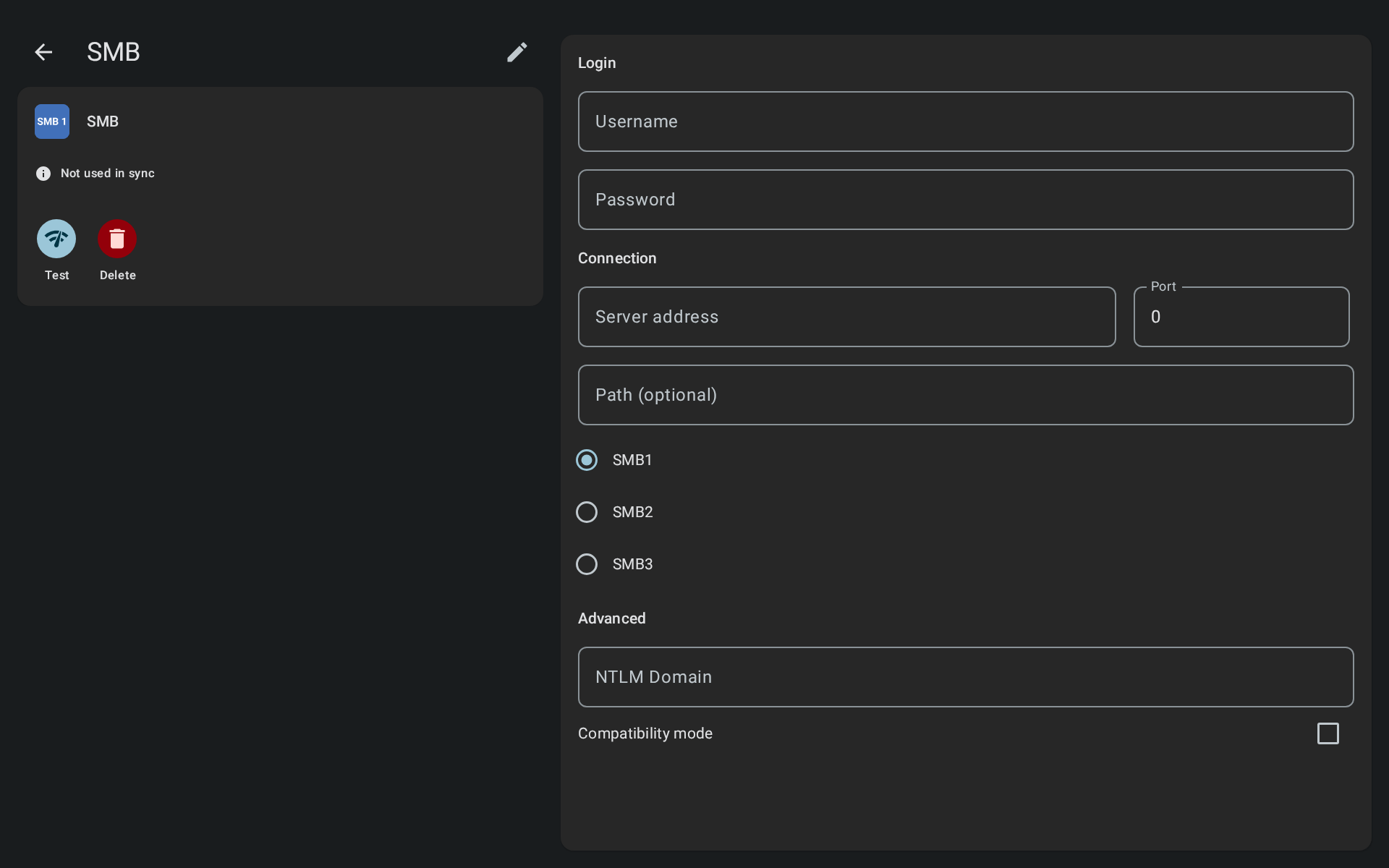
SMB1
The Server Message Block (SMB) is a network protocol that enables users to communicate with remote computers and servers.
- Login name: Your username for the server.
- Password: Your password for the server.
- Server address: The IP address or hostname of the server (without protocol or path), so like “192.34.243.2” or “my.server.com”.
- Port: The port to use.
- Path (optional): Optional path on the server that the connection should open on connection.
- NTLM domain (optional): Some Windows SMB servers may require this.
SMB1 is deprecated
SMb1 is considered deprecated and is disabled on newer Windows versions by default.
SMB2/SMB3
- Login name: Your username for the server. If using anonymous login, you may need to enter "guest" or other username.
- Password: Your password for the server.
- Server address: The IP address or hostname of the server (without protocol or path), so like “192.34.243.2” or “my.server.com”.
- Port: The port to use.
- SMB share name: The name of the SMB share you wish to connect to, this must be entered. For SMB2/3 FolderSync has no browse shares functionality.
- NTLM domain (optional): Some Windows SMB servers may require this.
- Enable DFS support: Check this if your SMB server supports DFS. If server does not support DFS, enabling this may cause errors.
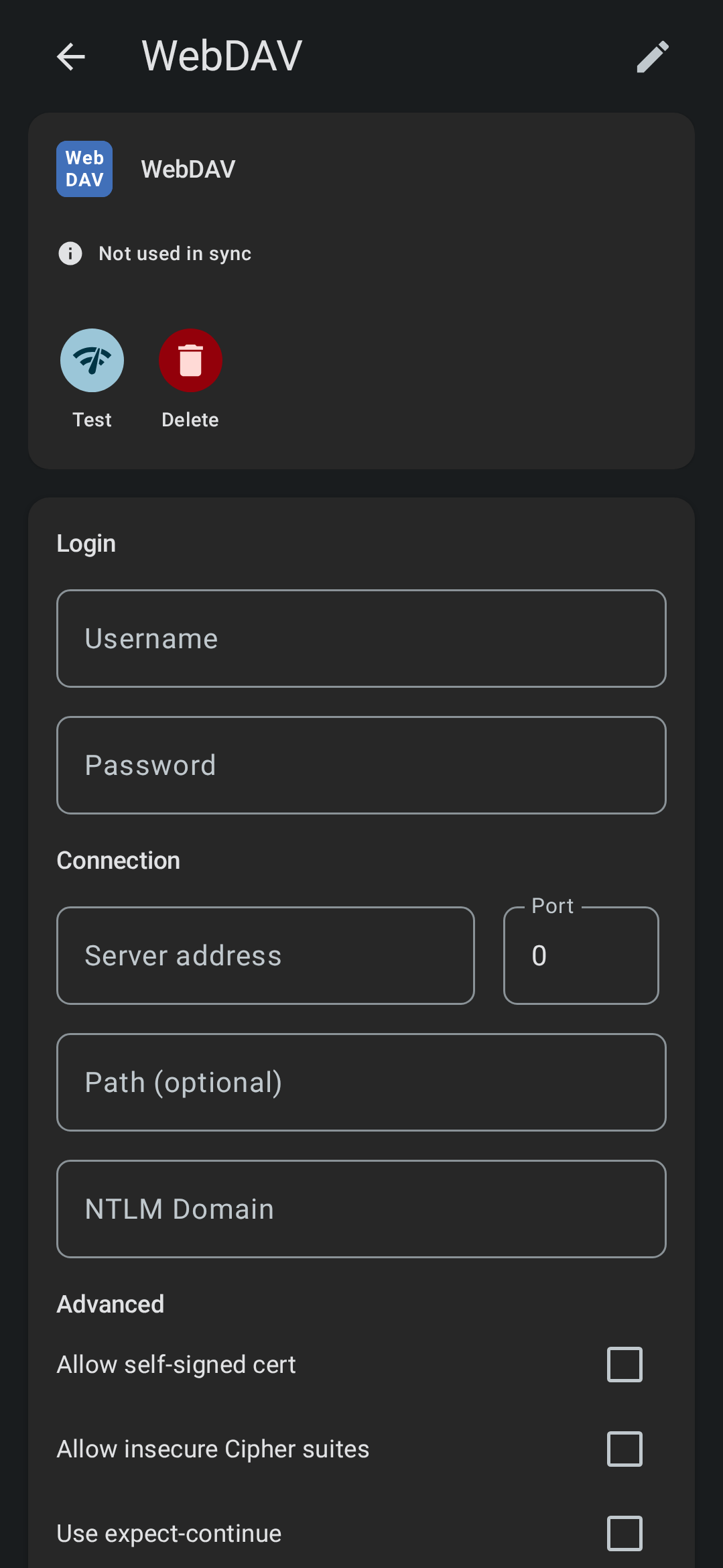
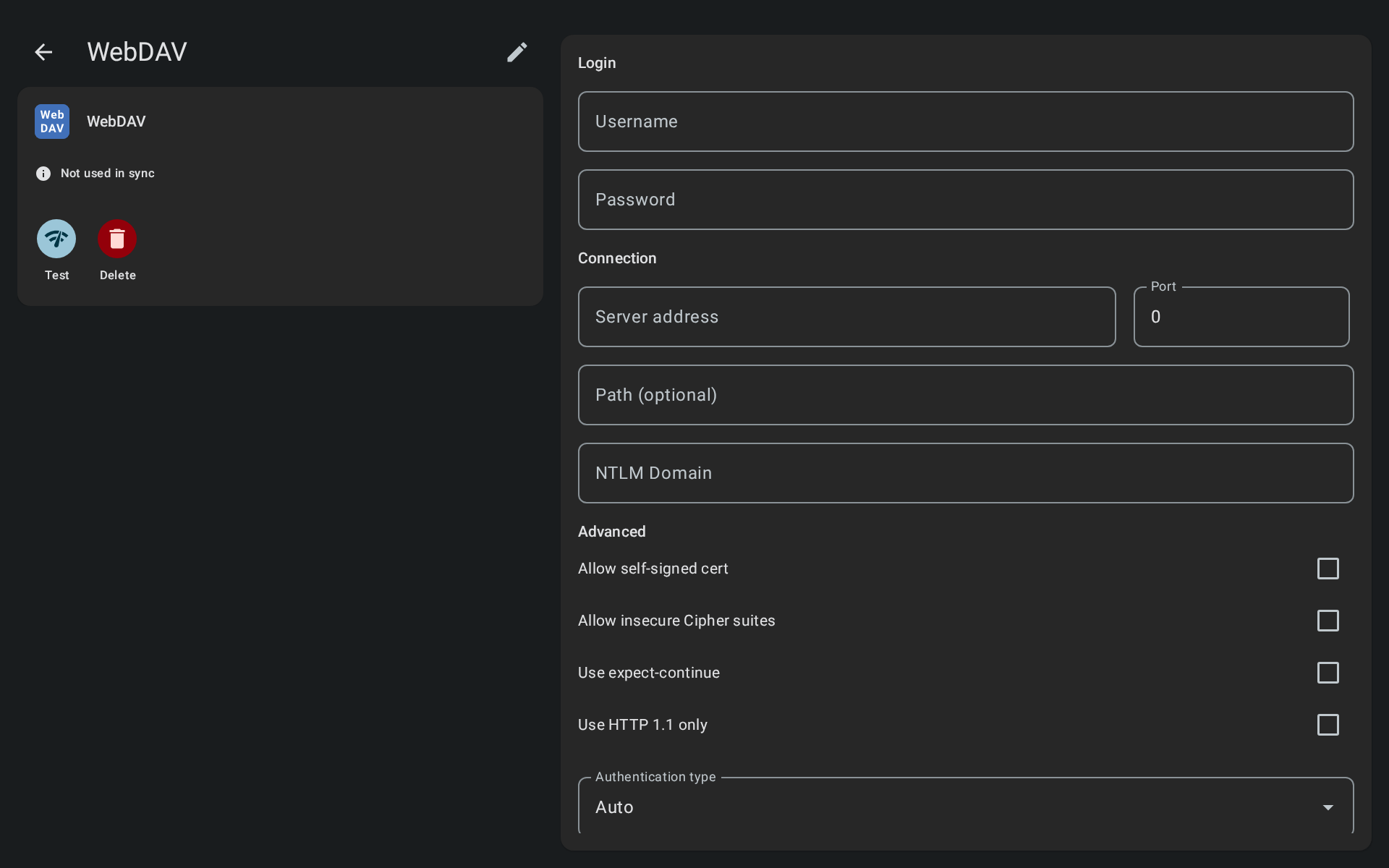
WebDAV/NextCloud/OwnCloud
WebDAV stands for "Web-based Distributed Authoring and Versioning". It is a set of extensions to the HTTP protocol which allows users to collaboratively edit and manage files on remote web servers.
NextCloud/OwnCloud
The NextCloud/OwnCloud account types automatically adds the WebDAV compatible path on the server to the configuration. If it doesn’t work for your server, please try to create a plain WebDAV account using configuration guide found in the NextCloud/OwnCloud documentation.
- Login name: Your username for the server.
- Password: Your password for the server.
- Server address: The IP address or hostname of the server (without protocol or path), so like “192.34.243.2” or “my.server.com”.
- Port: The port to use.
- Path (optional): Optional path on the server that the connection should open on connection.
- NTLM domain (optional): Some Windows WebDAV servers may require this.
- Allow self-signed cert: Enable if you use a self-signed SSL certificate on the server.
- Allow insecure Cipher suites: Some old servers have insecure ciphers for SSL encryption which you can choose to support.
- Use expect-continue: Some WebDAV servers doesn’t like this to be enabled.
- Use HTTP 1.1 only: Some WebDAV server has issues with HTTP/2 hence why you can force the connection to use HTTP 1.1.
- Authentication type: Use this to explicitly set the authentication type to use against the server.
- Client certificate: Optional client certificate to use for authentication.
- Certificate password: Password for client certificate if needed.
- Connection timeout: The time period within which a connection between a client and a server must be established before error is registered.
Only HTTPS supported
For WebDAV access FolderSync only supports HTTPS connections. Unencrypted HTTP is not supported. It is possible to use self-signed certificate although see warning below.
Allowing self-signed certificates
For security reasons this should not be enabled for servers unless you know what you are doing. If a server owner uses a self-signed certificate to provide HTTPS services, FolderSync cannot be certain that it is connected to the intended destination. For all FolderSync knows, malicious third-party could be redirecting the connection using another self-signed certificate bearing the same holder name. The connection is still encrypted, but does not lead to its intended target. In comparison, a CA-signed certificate prevents this attack because the app separately validates the certificate against the issuing CA. The attacker's certificate fails this validation.